Scottish Cyber Activity Report 2026
The Scottish Cyber Activity Report (SCAR) 2026 is the first of an annual publication from the Scottish Cyber Coordination Centre (SC3) giving a comprehensive, data-driven assessment of cyber activity across Scotland's public sector.
2. Incidents
The Scottish public sector experiences cyber activity regularly. Between 2018 and early 2026, SC3 managed, coordinated or engaged in responses to 183 incidents, ranging from low impact denial of service attacks to widespread ransomware campaigns and major network compromises. These incidents have affected organisations across every sector: local authorities, health bodies, central government, education, and the private suppliers that the public sector services depend. Each incident has generated learning and collectively, they paint a picture of Scotland’s cyber maturity and the capabilities required to respond effectively.
This section examines the threat landscape, preparedness across the sector, and the key lessons emerging from incident response operations.
2.1. Threat Intelligence and Vulnerability Coordination
Effective incident response begins long before an attack occurs. It depends on organisations having timely access to threat intelligence, the tooling to detect threats, and the capacity to act on warnings when they arrive.
SC3 distributes threat intelligence through two primary channels. CREW (Cyber Resilience Early Warning) notices and TIPR (Threat Intelligence Priority Reporting) In the last year, SC3 issued 60 CREW notices and 23 TIPR notices, reaching hundreds of recipients across the sector. Additionally, SC3 has published 83 reports and triaged 119 vulnerability disclosures, providing a steady stream of information to help public sector organisations understand and mitigate emerging threats.
The impact of this work is evident in the Cyber Resilience Assessment. Of the organisations surveyed, 97% reported that they receive threat intelligence from SC3 or other sources, with 86% subscribed to the SC3 daily threat report, suggesting a high level of uptake and value from the services SC3 provide in relation to threat intelligence. However, receipt of threat intelligence is only the first step. The CRA found that 89% of organisations use at least one tooling option for threat detection which is a significant capability, whilst 91% confirmed they can act on threat intelligence received. This suggests a generally mature level of threat intelligence integration across the sector, though the gap between those receiving intelligence and those able to act on it should not be overlooked.
Vulnerability coordination is equally important. SC3’s work to identify and disclose vulnerabilities affecting multiple organisations has prevented exploitation and enabled the sector to patch in a coordinated manner. This work is particularly critical in the context of supply chain risk, where vulnerabilities in widely deployed software can affect hundreds of organisations simultaneously.
The above shows the level of preparedness for the sector is strong when identifying threats and demonstrates that organisations are not only receiving and consuming intelligence but are also increasingly equipped with the tools or means and operational capacity needed to detect, prioritise, and act on those threats. Together with SC3’s vulnerability coordination work, this reflects a sector that is building resilience proactively rather than reactively, ensuring that early warning and threat detection are in place to combat the ever-increasing cyber activity seen across the sector.
2.2. Incident Preparedness
Preparedness is foundational to cyber resilience. SC3 recommends that public sector organisations invest in incident response planning, business continuity planning, staff training, and access to specialist incident response capability. Evidence suggests that organisations that have made these prioritisations in preparing for incidents recover faster and experience less impact than those that have not. The CRA provides detailed evidence of preparedness across the sector.
2.2.1. Preparedness in Numbers
Most organisations surveyed reported having incident response plans in place.
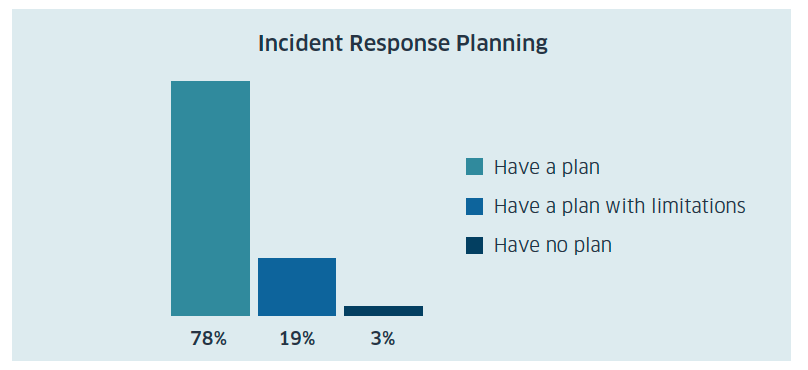
Incident Response Planning
- 78% Have a plan
- 19% Have a plan with limitations
- 3% Have no plan
This represents a relatively mature baseline. However, the finding that nearly one in five organisations have acknowledged gaps in their plans is significant. Complete loss scenarios where an organisation loses access to core digital systems for an extended period are increasingly realistic and demand specific planning. These scenarios are a significant burden to any sector, and in the public sector the significance cannot be understated. Business continuity and disaster recovery planning show similar patterns.
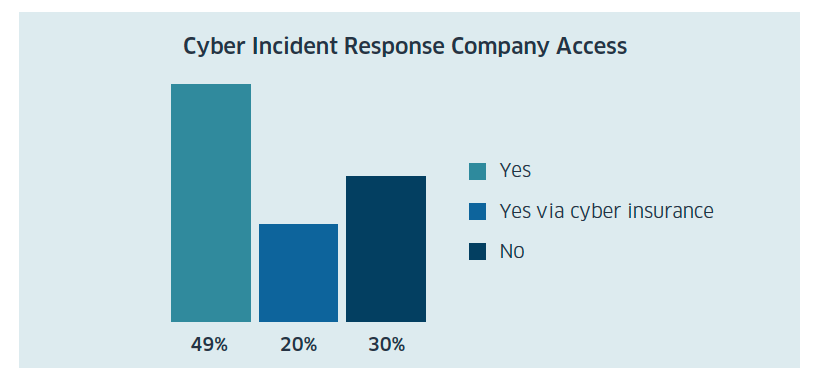
Cyber Incident Response Company Access
- 49% - Yes
- 20% - Yes via cyber insurance
- 30% - No
A critical component of incident preparedness is access to specialist cyber incident response (CIR) and forensic capability.
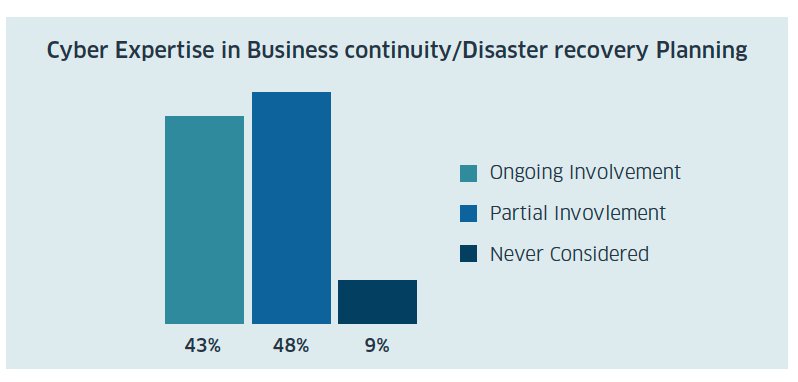
Cyber Expertise in Business continuity / Disaster recovery Planning
- 43% - Ongoing Involvement
- 48% - Partial Involvement
- 9% - Never Considered
When organisations without a CIR provider experience a major incident, they must rapidly identify and engage external providers, a process that consumes valuable time and may leave them without guidance during the critical early hours of an incident.
SC3 publishes several templates for incident response and playbooks for specific incidents.[5] These documents are designed to help organisation in the sector begin to plan for a cyber incident. They provide best practice advice and guidance, and prove as a starting point for a comprehensive and detailed plan. The sector’s engagement with SC3’s resources is evident in website download statistics. The Generic Cyber Incident Response Plan has been downloaded 386 times, the Public Sector Incident Response Plan 255 times, and sector-specific playbooks (for phishing, ransomware, malware, supply chain, denial of service, and data loss) have collectively been downloaded over 1,100 times. These numbers suggest that many organisations are downloading structured guidance, though downloading and implementing are distinct activities. It also suggests that the documents published by SC3 are received by a wider audience than just the public sector, serving the wider resilience of the private and third sectors.
2.3. Incident Response
2.3.1 The Incident Coordination and Response Workstream
The SC3 Incident Response Workstream focuses on delivering rapid and consistent coordination across multiple agencies during significant or national‑level cyber incidents. Its core purpose is to support affected organisations as they manage and recover from cyber events, while ensuring that essential information is communicated to stakeholders when required.
2.3.2 Incidents in Numbers
Between 2018 and early 2026, 183 incidents have been reported to SC3. A breakdown of recent incidents can be seen at the table below.
| Year | Major | Minor | Total |
|---|---|---|---|
| 2023 | 5 | 32 | 37 |
| 2024 | 4 | 32 | 36 |
| 2025 | 5 | 34 | 39 |
SC3 defines a major incident as one which requires a multi-agency response, beyond a routine situational awareness coordination. The balance of severity has been similarly steady, with major incidents representing roughly 12-14% of the annual total. Whilst many incidents do not reach the threshold of significance where national response arrangements led by the UK Government’s National Cyber Security Centre would be required, minor incidents still impose operational disruption and consume resources that smaller organisations do not have readily available.
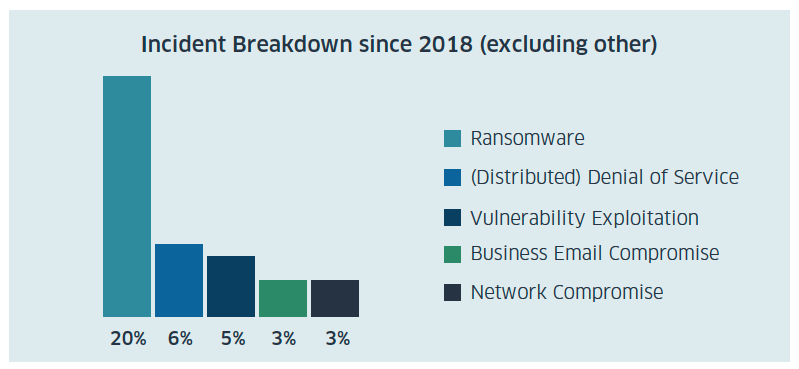
Incident Breakdown since 2018 (excluding other)
- 20% - Ransomware
- 6% - (Distributed) Denial of Service
- 5% - Vulnerability Exploitation
- 3% - Business Email Comprimise
- 3% - Network Comprimise
Of the threats seen, ransomware is the most prevalent, accounting for 37 incidents. This aligns with the NCSC’s 2025 Annual Review, which identifies ransomware as the most pressing cyber threat to the UK. The NCSC reports that over 6,500 organisations globally were published on dark web leak sites in the year to August 2025, with the UK the fourth most targeted country. The emergence of ransomware-as-a-service platforms and malware-as-a-service marketplaces has lowered the technical barriers to entry, making this threat accessible to a widening pool of threat actors.
For comparative context, the NCSC’s 2025 Annual Review reports that its incident management team handled 429 incidents requiring direct support in the year to August 2025, from 1,727 tips received. Of these, 204 were classified as nationally significant which amounts to a 130% increase on the previous year’s 89, and 18 were classified as highly significant, a 50% increase.
The UK now faces an average of four nationally significant cyber-attacks per week. At UK level, the proportion of incidents classified as nationally significant has more than doubled in a single year, rising from 21% to 48% of the NCSC’s caseload. By contrast, SC3’s proportion of major incidents has remained stable at approximately 13% across 2023, 2024, and 2025, noting SC3’s specific remit of the public sector in Scotland.
Contact
Email: SC3@gov.scot